In the world of NestJS, Data Transfer Objects (DTOs) are often treated as a boilerplate necessity—a simple class we create to satisfy the compiler.
However, if you are building complex systems like multi-tenant e-commerce platforms or AI-integrated backends, your DTOs are actually the first line of defense for your application’s integrity.
Why DTOs Matter More Than Ever
A DTO defines how data is sent over the network. By using classes coupled with decorators, NestJS allows for runtime validation, ensuring that the “junk data” never even hits your service layer.
The Standard Approach: Class-Validator
Most developers start with class-validator. It’s intuitive and integrates natively with the NestJS ValidationPipe.
import { IsString, IsEmail, MinLength } from 'class-validator';
export class CreateUserDto {
@IsString()
name: string;
@IsEmail()
email: string;
@MinLength(8)
password: string;
}
While effective, this approach can sometimes lead to “Decorator Hell,” where your DTO classes become bloated with metadata that is hard to reuse outside of the NestJS context.
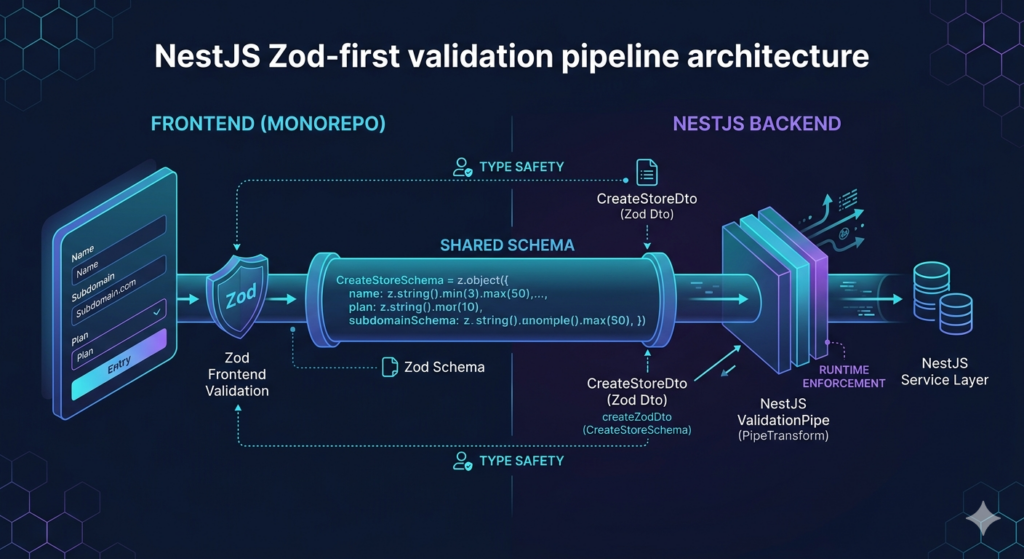
The “Zod-First” Revolution
As we move toward more unified architectures (like monorepos), many developers are shifting toward Zod for DTO validation. The “Zod-first” approach allows you to define a single schema that can be shared between your backend validation and your frontend forms (e.g., in a Next.js storefront).
Implementing Zod DTOs in NestJS
To use Zod, you can leverage the nestjs-zod library or create a custom pipe. This allows for incredibly powerful, functional validation logic that feels more like TypeScript and less like annotation.
import { createZodDto } from 'nestjs-zod';
import { z } from 'zod';
const CreateStoreSchema = z.object({
name: z.string().min(3).max(50),
subdomain: z.string().toLowerCase().regex(/^[a-z0-9-]+$/),
plan: z.enum(['LAUNCH', 'SCALE', 'ENTERPRISE']),
});
export class CreateStoreDto extends createZodDto(CreateStoreSchema) {}
Key Benefits:
-
Deep Type Safety: Infers TypeScript types directly from the schema.
-
Transformation: Automatically handles data casting (e.g., converting a string to a Date object).
-
Shared Logic: Use the exact same
CreateStoreSchemain your frontend dashboard to show real-time validation errors.
DTO Strategies for Multi-Tenant Systems
When building platforms that handle sensitive data across different “tenants” or “merchants,” your DTOs should be context-aware.
1. Partial Types for Updates
Don’t rewrite your DTOs for update operations. Use the PartialType utility to keep your code DRY (Don’t Repeat Yourself).
export class UpdateStoreDto extends PartialType(CreateStoreDto) {}
2. Stripping Sensitive Fields
Always ensure your ValidationPipe is configured to whitelist: true. This prevents “over-posting,” where a malicious user tries to inject a role: 'admin' field into a DTO that shouldn’t have it.
3. Handling AI Metadata
If your application integrates AI agents, your DTOs may need to handle structured “tool-calling” data. Using Zod’s passthrough() or strict() modes helps you control exactly how much “extra” data an AI agent is allowed to send to your API.
Best Practices for 2026
-
Always use Classes: Even if using Zod, wrap schemas in classes so the NestJS IoC container can recognize them for Dependency Injection and Swagger documentation.
-
Map, Don’t Leak: Use DTOs to map your Database Entities to API Responses. Never return your raw Database Entity (with password hashes or internal IDs) directly to the client.
-
Automate Documentation: Ensure your DTOs are decorated for
@nestjs/swagger. This turns your DTOs into a living API contract that frontend teams (and AI agents) can read easily.
Choosing a Validation Library for NestJS
Choosing between class-validator and Zod often comes down to your project’s architecture and how much you value code sharing.
Class-Validator
-
Syntax: Uses Decorators and Annotations directly on your class properties.
-
Type Inference: Mostly manual; you must define the class and the types separately.
-
Frontend Sharing: Difficult, as it relies on NestJS-specific decorators that don’t always play nice with frontend frameworks like React or Vue.
-
Complexity: Simple and intuitive for those used to Object-Oriented Programming.
Zod
-
Syntax: Uses a Functional Schema approach to define data shapes.
-
Type Inference: Automatic; the TypeScript types are inferred directly from your schema definitions.
-
Frontend Sharing: Seamless, making it the “gold standard” for monorepos where the same schema validates both your frontend forms and backend API.
-
Complexity: Highly Powerful, offering advanced features like data transformation and complex refinements.
By mastering DTOs, you aren’t just “fixing types”—you’re building a secure, predictable, and scalable gateway for your entire application.
Quote of the Day:
“Always code as if the guy who ends up maintaining your code will be a violent psychopath who knows where you live.” — John Woods
Useful links below:
Let me & my team build you a money making website/blog for your business https://bit.ly/tnrwebsite_service
Get Bluehost hosting for as little as $1.99/month (save 75%)…https://bit.ly/3C1fZd2
Best email marketing automation solution on the market! http://www.aweber.com/?373860
Build high converting sales funnels with a few simple clicks of your mouse! https://bit.ly/484YV29
Join my Patreon for one-on-one coaching and help with your coding…https://www.patreon.com/c/TyronneRatcliff
Buy me a coffee 




